I know everyone is talking about the Signal chat where a bunch of warmongers stupidly invited the editor of The Atlantic to join in, but I have to tell you that these things are always insecure, and I have some personal experience with that.
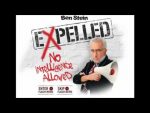 Remember when the Expelled movie was a topic of conversation? They were doing all these press tours and radio interviews touting that stupid movie, and one of their events was a conference call in which the various people involved (Ben Stein, Mark Mathis, etc.) were calling in to promote the movie, and invited people to call in and listen to their propaganda. Well, I was involved, unfortunately, and I called in to hear what they were going to say, but accidentally found out how to join in, not just to listen, but to speak. I ‘hacked’ their system and crashed the event!
Remember when the Expelled movie was a topic of conversation? They were doing all these press tours and radio interviews touting that stupid movie, and one of their events was a conference call in which the various people involved (Ben Stein, Mark Mathis, etc.) were calling in to promote the movie, and invited people to call in and listen to their propaganda. Well, I was involved, unfortunately, and I called in to hear what they were going to say, but accidentally found out how to join in, not just to listen, but to speak. I ‘hacked’ their system and crashed the event!
Some of you know that the producers of Expelled had a conference call this afternoon…a carefully controlled, closed environment in which they would spout their nonsense and only take questions by email. I listened to it for a while, and yeah, it was the usual run-around. However, I dialed in a few minutes early, and got to listen to a tiresome five minutes of Leslie and Paul chatting away, during which time they mentioned the secret code (DUNH DUNH DUNNNNH!) for the two way calls. I know. Sloppy, unprofessional, and stupid, but that’s the way they work.
So … I redialed. (DUNH DUNH DUNNNNH!)
Then I listened along quietly until I could take no more.
There were links about this, and even a recording of what I said in response to their nonsense, but it’s all dead links now, I’m sad to say.
Don’t trust the tech to protect your conversations! You never know when some nefarious rascal might eavesdrop.


Ahhhh… Better times.
So, use code phrases if you’re texting about starting an insurrection?
Insurrection? No insurrections here. We’re planning an ice cream social. Bring your garden rakes with full clips of pastry frosting, and don’t forget the forceps and extension cords!
So much for the internet is forever eh? Pity.
Nothing the Wayback Machine or other archives could save? Screenshots, sources somewhere or as evanescant as a mayflies snapchat photo?
PZ, if you’re alleging the Signal protocol’s crypto and Signal’s implementation of said crypto are insecure, you have to back that up with evidence. Signal’s crypto is a gold standard for E2EE and benefits from intense scrutiny from researchers; in practical terms it’s probably the best option we have for end-to-end encrypted chats. More likely is that the endpoints were carelessly set up (clearly, in retrospect) or that at least one of the devices using it was compromised.
It’s fair to say a bunch of warmongers invited a fellow warmonger. Let’s not forget Jeffrey Goldberg was one of the biggest cheerleaders for invading Iraq in 2003.
Exercise some basic discretion about using a side-channel-ridden smartphone and inviting trustworthy people who know how to use encrypted chat properly, but the Signal software is not the weak link there. I trust it to do a reasonably good job protecting message contents from eavesdroppers between endpoints.
“Alleging”? As everyone knows, cryptography can’t be any more secure than the people using it. Signal could have been technically impregnable…yet it was penetrated. Just like that conference call.
A beholder, # 5: Any security can be penetrated. You just have to find the weak point.
@beholder, #5: I think we’re not saying that Signal was the weakest link here. The weakest link was the unqualified officials using it. The second weakest link was the personal devices Signal was running on. Signal is fairly close to the last in the list, but it’s far from blameless.
Even if Signal crypto is unbreakable, there’s an amazing amount of information you can get through traffic analysis – with large, frequent message exchanges about 2 hours before something happens. That’s why exchanges such as these are supposed to only be done on classified networks. As is, anyone could “misconfigure” their BGP endpoint to monitor such traffic and determine the rough timing of the next attack.
<sarcasm&rt; Chat systems (phone, text, whatever) don’t reveal secrets. People reveal secrets. </sarcasm>
@5: Technologically, the type of encryption system Signal uses is in a general sense the best that’s employed commercially for general use. The problems are:
• “employed commercially”
• “general use”
• “users not allowing unauthorized individuals to participate”
not to mention
• “wtaf were these morons doing discussing plans for an impending operation outside a secure conference room????????????”
Oops. I apologize to all persons with “verified IQ scores” between 50 and 70 — the old criminal-law standard for “moron” — because they’ve generally got better judgment than these cretins.
Back in University one of my text books was by Bruce Schneier… not long after he published Applied Cryptography which was the standard text for years, he was already commenting how how we basically had cryptographic algorithms that would last the expected lifetime of the universe, but the problem was that people rarely implemented or used them properly. For example, in one of the early SSL implementations back in the Netscape Navigator days, you could basically run timing attacks on the server to figure out the key by seeing how quickly it said you had the wrong key.
My professor for the network security course (Dr. Gord Agnew) actually went through things like traffic analysis and timing analysis and how to harden your system against those.
Of course, no hardening will help against someone who’s willing to hand off their access information to someone else without double-checking. Social Engineering is all about accessing the most common weak point in any security system: the people who have to use it on a day-to-day basis.
Social Engineering is indeed the biggest vulnerability, but in this case it’s clearly a matter of
(a quotation from the play The Maid of Orleans by Friedrich Schiller:) “Mit der Dummheit kämpfen Götter selbst vergebens”: “Against stupidity the gods themselves contend in vain”.
(https://en.wikipedia.org/wiki/The_Gods_Themselves)
Ahhh… I do remember the good old days, when Richard Dawkins still was one of the good old guys… I miss those days…
Their putative promotional music video “Beware the Believers” is still up: https://youtu.be/eaGgpGLxLQw
(posted on the correct thread now)
Just call me the Master of Google-Fu.
Transcript:
https://web.archive.org/web/20080331124600/http://skepchick.org/blog/?p=1190
Wax on, wax off.
No wait.. that’s karate.
I mean um,…grasshopper.
Actually, it’s so hilarious, with so much flailing, I’m just gonna post it.
@ ^ Silentbob : Thanks for the transcript and link there. Appreciated.
@ ^
Mate, it’s comedy gold. It needs to be preserved. ;-)
I especially love, “If we have a question for PZ we can invite him back on”. X-D
Narrator: They never had a question for PZ.
I’ve posted this elsewhere, but it’s appropriate:
For more than a decade, I worked as a contractor on a military project that provided web portal services. The military understood that Facebook existed, but Facebook is not secure. So to help families of Servicemembers keep up to date on what was going on with their Units (when are they deploying, coming back, etc.) our systems were developed that would provide a way for this information to be posted securely.
Now, OPSEC information was never to be posted on our sites, either, but things like the flight schedule for returning Servicemembers is still sensitive and should not be bandied about. And even more importantly, that information would not be mined for data and sold to advertisers and who knows who else. The military would have control over it and could order it all to be shut down at any moment if there was a problem. It would be military people who were in control.
So suffice to say that when I hear that members of the military and executive branch of the government were using public apps to discuss sensitive information, I am filled with disgust. There’s a reason that these restricted channels of communication are created. It was like pulling teeth with some Units to get them to stop using Facebook and use the system that was developed for them. One of my military contacts would routinely go onto Facebook pages for Units in their purview and find not merely sensitive information but actual OPSEC that should NEVER be posted anywhere.
There is no excuse. There is a dedicated system within the military for these types of communications. There is never any reason to use commercial apps for this.